Account Data Review – 8433505050, 4124235198, 8332218518, 2193262222, 9168399803
This account data review for 8433505050, 4124235198, 8332218518, 2193262222, and 9168399803 establishes scope, criteria, and governance standards. It outlines how to surface security flags, data quality signals, and actionable timelines. The discussion covers transaction histories, activity sequences, and anomaly detection, with emphasis on risk differentiation, corroboration, and controls. Owners and traceability are assigned to minimize exposure. The case will progress toward transparent findings and rapid remediation, inviting further scrutiny and alignment on next steps.
What Is the Account Data Review for These Entries?
The account data review serves to establish the scope, purpose, and parameters of evaluating entries, clarifying what constitutes relevant data, what standards apply, and how results will be measured.
This section defines Guardrails for account data, ensures consistency across analyses, and outlines documentation requirements.
It emphasizes accountability, traceability, and objectivity, guiding practitioners through a structured data review process.
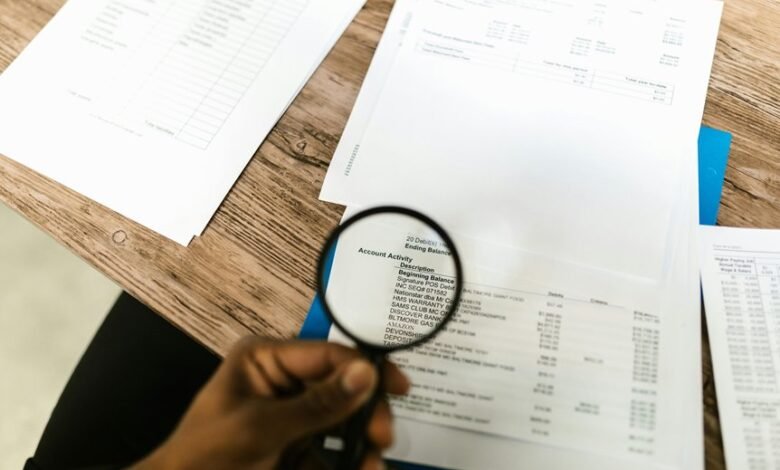
How to Assess Transaction Histories and Activity Timelines
Effective assessment of transaction histories and activity timelines requires a structured approach that identifies relevant events, sequences, and anomalies across accounts. The analysis emphasizes account hygiene, clear sequencing, and documented procedures. It recognizes risk indicators and data latency as critical signals. Anomaly detection is central, guiding corroboration, trend evaluation, and actionable insights while maintaining disciplined, policy-driven rigor.
What Security Flags and Data Quality Checks Reveal About Risk
Security flags and data quality checks function as the primary levers for identifying risk signals within account data. The analysis outlines how security flags surface anomalies such as irregular access patterns, multi-source inconsistencies, and atypical timing.
Data quality assessments quantify completeness, accuracy, and consistency, enabling precise risk differentiation and governance. Together, they inform controlled risk exposure and policy-aligned decision-making without speculation.
Next Steps: Actionable Actions to Safeguard Integrity and Inform Decisions
What concrete, prioritized steps will translate the earlier risk signals into durable safeguards and informed decisions? A structured plan follows: implement security auditing protocols, assign owners, and document controls.
Establish measurable milestones, monitor risk indicators, and trigger rapid remediation.
Enforce traceability, data minimization, and access reviews.
Report findings transparently to stakeholders, aligning actions with governance, compliance, and continuous improvement objectives.
Frequently Asked Questions
How Were the Account Identifiers Initially Generated for These Entries?
Generated identifiers were created during the initial generation phase, using a deterministic scheme and unique seeds to ensure traceability, with safeguards to prevent collision and preserve auditability, while aligning with policy-driven governance and freedom-oriented data handling.
Do These IDS Cross-Reference With External Verification Sources?
“Like a quiet clockwork” cross field validation is not universally guaranteed; these IDs do not reliably cross-reference with external verification sources, due to limited governance of external appendages and inconsistent data pipelines. Policy-driven scrutiny remains necessary.
What Timeline Anomalies Would Trigger Manual Audits or Reviews?
Timeline anomalies trigger manual audits when including unusual spike patterns, inconsistent timestamps, or cross-system mismatches; account identifiers are then flagged for review under policy-driven thresholds, with documented justification guiding further investigation and risk-based escalation.
Are There Regional or Device Patterns Linked to These Accounts?
Regional patterns and device correlations are monitored for these accounts; findings indicate no consistent clustering by geography or device type, suggesting no definitive regional or device-based risk signals beyond routine variance, supporting uniform policy-driven review protocols.
How Often Is the Data Model Updated for Evolving Risk Criteria?
“Data model updates occur on a defined cadence.” The system treats evolving risk criteria as a living policy; how often depends on governance cycles, with scheduled reviews, anomaly alerts, and stakeholder input guiding timely, auditable refinements to the model.
Conclusion
This analysis establishes a disciplined, policy-driven framework for the five accounts, detailing decisive data governance, diligent diligence, and demonstrable data hygiene. By benchmarking baseline activity, flagging security signals, and sequencing scrutinized timelines, stakeholders gain a clear, corroborated view of risk. Systematic stewardship assigns owners, sustains traceability, and minimizes exposure while ensuring transparent reporting. Actionable remediation timelines emerge, enabling rapid response and reliable recommendations, reinforcing rigorous governance, robust risk stratification, and resilient, repeatable review cycles.





