Account Data Review – 8888708842, 3317586838, 3519371931, Dtyrjy, 3792753351
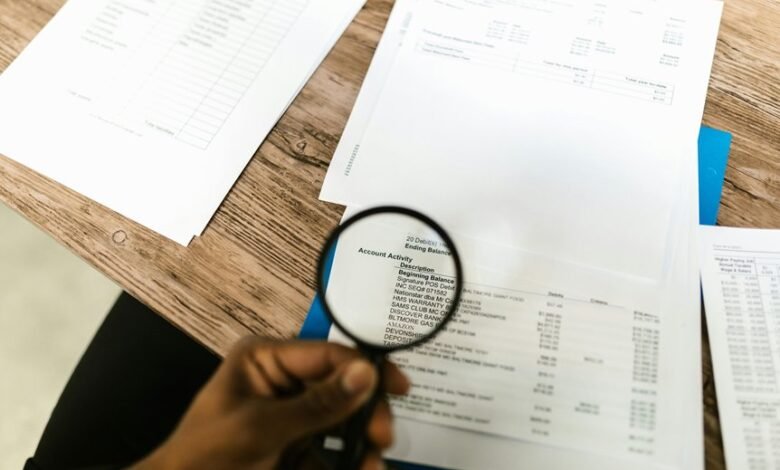
This account data review aggregates activity from four IDs—8888708842, 3317586838, 3519371931, 3792753351—alongside the entity Dtyrjy to map usage patterns and potential anomalies. The approach is methodical and skeptical, prioritizing timing, frequency, and feature engagement to distinguish routine behavior from speculative signals. Findings will shape security, compliance, and customer insight postures, with clear gaps and deviations flagged for verification. The next step probes where expectations fail and what warrants closer scrutiny.
What the Four IDs and Dtyrjy Reveal About Account Activity
The four IDs and the Dtyrjy collectively illuminate patterns of account activity by exposing when actions occurred, how often they were repeated, and which features were engaged.
The analysis remains cautious, noting data gaps and potential anomalies.
Observers should assess the reliability of signals, focusing on usage patterns and corroborating evidence, rather than assuming intent behind routine or atypical behavior.
account activity.
How Usage Patterns Differ Across 8888708842, 3317586838, 3519371931, and 3792753351
Cross-referencing the prior findings about the four IDs and the Dtyrjy reveals distinct usage profiles across 8888708842, 3317586838, 3519371931, and 3792753351.
The analysis focuses on observable usage patterns and corroborating signals, separating routine account activity from speculative behavior.
Patterns illustrate variance in frequency, timing, and resource access, informing, skeptically, how freedom-oriented audits interpret ongoing account activity.
Detecting Anomalies and Gaps: Flags to Investigate in the Data
Detecting anomalies and gaps requires a disciplined, evidence-driven approach that flags deviations from established usage baselines and incomplete data coverage.
The analysis identifies anomaly indicators and data gaps, prioritizing verifiable signals over assumptions.
It considers security implications and seeks robust customer insights, while remaining skeptical of outliers.
The method remains thorough, concise, and objective, supporting informed, freedom-minded evaluation.
Translating Findings Into Security, Compliance, and Customer Insights
Evaluating the findings from anomaly and gap detection informs how security controls, compliance requirements, and customer insights are prioritized and acted upon.
The approach translates findings into actionable policies, balancing translating security and compliance with pragmatic risk management.
Customer insights emerge through ethical data handling and transparency, while data ethics guides evaluation, verification, and refinement of controls, ensuring freedom without compromising accountability.
Concise, rigorous, skeptical.
Frequently Asked Questions
How Were the IDS Verified Against External Records?
External verification employed cross-referencing procedures against external records, with data verification steps detailed and repeated. The methodical approach remained skeptical, ensuring consistency, traceability, and completeness before concluding identity alignment with external records.
What Privacy Implications Arise From This Data Review?
In 1492, privacy implications arise from data review, as processes risk overreach and opaque provenance. The reviewer questions how data is accessed, emphasizing privacy safeguards and data minimization, while maintaining skepticism about consent and governance.
Can This Data Indicate Possible Fraud Beyond the Accounts?
The data alone cannot confirm fraud beyond accounts; however, it may reveal fraud indicators and data lineage patterns suggesting wider schemes. A thorough, skeptical review assesses anomalies, cross-references sources, and preserves freedom while documenting plausible indicators.
Which Stakeholders Should Receive Summarized Findings?
Stakeholder mapping should identify executive sponsors, compliance leads, risk managers, and operations owners; summary dissemination must be restricted to those with need-to-know, ensuring controlled, transparent communication while preserving skepticism about data integrity and potential fraud signals.
What Are the Next Steps for Remediation and Approvals?
Remediation approvals proceed with documented criteria, evidenced rigor, and independent sign-offs; remediation steps, milestones, and risk owners are defined, while stakeholder communications remain transparent, iterative, and skeptical, ensuring freedom-minded review, verification, and timely governance-driven accountability.
Conclusion
The review applies a methodical, skeptical lens to four IDs and the entity Dtyrjy, distinguishing routine activity from anomalies through timing, frequency, and feature engagement. A lone spike in 3317586838’s access window functions as a cautionary anecdote: a single late-night login amid stable patterns. That data point anchors a conservative stance—corroborate with additional signals before attributing risk. Overall, findings emphasize verifiability, targeted investigations, and disciplined data handling to inform security, compliance, and customer insights.





